Cyber threats and attacks usually accompany armed conflict these days. And that certainly the case with the current war in the Ukraine as both the National Cyber Security Centre (NCSC) and the Information Commissioners Office (ICO) are warning of increased cyber security risks.
Where’s the threat?
The threats come from three main activities:
- Cyber attacks aimed directly at the conflict participants. ESET uncovered a destructive attack against computers in Ukraine that started around 14:52 on February 23rd, 2022 UTC. This followed distributed denial-of-service (DDoS) attacks against major Ukrainian websites and preceded the Russian military invasion by a few hours. These types of attack can also result in infections to similar computers or applications in other countries.
- Cyber attacks aimed at those countries and organisations that sympathise or support the Ukraine such as the UK and other European Counties, and
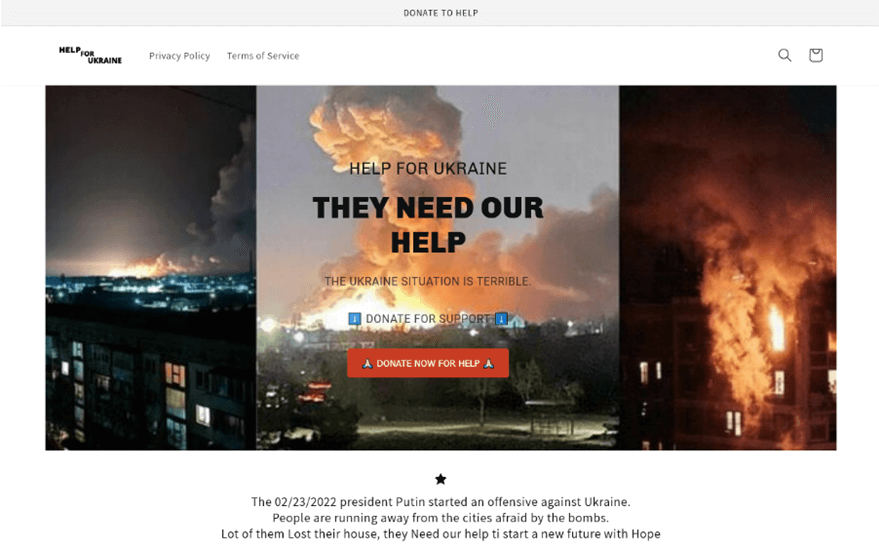
- Spoof websites and phishing emails aimed at the public. ESET researchers have spotted a bevy of websites (see the example below) that solicit money under the guise of charitable purposes. They tend to be on a similar theme, making emotional but nonetheless fake appeals for solidarity with the people of Ukraine or urging the public to help fund the country’s defence efforts. Also, stay alert for emotional pleas for help that may land in your email. Other similar ploys that aim to get the victims to donate some Bitcoin are floating around on Twitter and other social media.
What actions should you take?
During this period of known heightened risks, the NCSC recommends a suite of activities to ensure your defences are strong and you’re prepared in case of a cyber security incident. Where we are your IT Provider, we have increased our vigilance and the speed at which we push out software patches and updates.

- Phishing awareness: Ensure your staff know to spot phishing emails and how to report them. In addition, consider using email security software
- Check system patching: Software updates and patches are a key way to ensure potential system vulnerabilities are addressed as quickly as possible. Ensure your systems are set to accept updates from system vendors such as Microsoft and Apple.
- Verify access controls: Check that your staff are using complex and unique passwords and comply with your password policy. All applications, particularly email, should be set to use multi-factor authentication. Review who has access to your applications, particularly administrator access, and close old or unused account.
- Ensure defences are working: Make sure your security (anti-virus) software is running and up to date. Check firewall and router settings are appropriately configured.
- Review backups: Backups are a key, and sometimes the only way, to recover from a ransomware attack. So check your backups are working as they should be and you know how to restore files and systems if you need to.
- Review Third party access: Who else has access to your systems – contractors, agency workers, suppliers? Check that they also have all necessary security defences in place to a level at least as good of your own. And finally …
- Dig out your Incident plan: Ensure that your plan is current and has clear on who has authority to make decisions. Make sure it has actions to take in case of a security incident.
The risks and threats we face are nothing like the folk in harm’s way in the Ukraine, but nevertheless we all need to ensure our cyber security defences are prepared and operating effectively.
If you need any help or guidance, please call us on 01428 770 290.

